Discover the critical steps healthcare providers can take to protect patient data against rising cyber threats. From encryption to third-party risk management, learn how to build a robust defense.
Security
Cloud Native Challenges – Cloud native is a modern approach to building and running software applications that exploit the flexibility,…
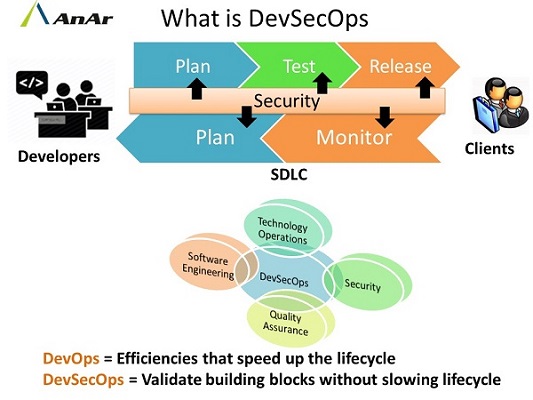
SecOps comprises the cooperation of security and IT operations teams. They have their individual responsibilities yet are jointly responsible for…
Cloud native application is a lightweight container based virtual and shared infrastructure. We develop cloud native applications in different programming…
Introduction: Over a period, almost all categories of businesses and sizes of companies have selected Windows Server and SQL Server…
Outsourcing is crucial part of modern day business. Every industry tries to cut the expense ratio for profitability and sustainability….
Software is traditionally divided into two categories: packaged or custom. Custom software, also known as “Bespoke” software, is a type…
Software Security In today’s world everyone is very concerns about privacy. We like to ensure data about ourselves is not…
You must be aware of the exponential growth in machine data over the last decade. It was partly because of…
Enterprise mobility is what Internet was a couple of decades back for enterprise and its transitions in terms of technology…
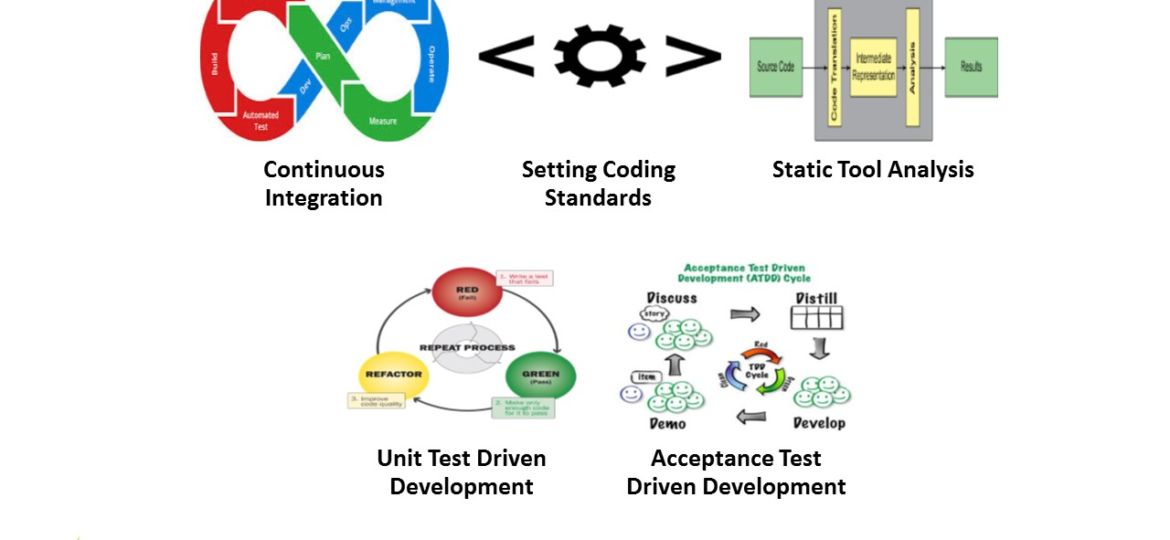
There is a saying that quality is a free commodity provided one invests in improving it. The major problem with the legacy…
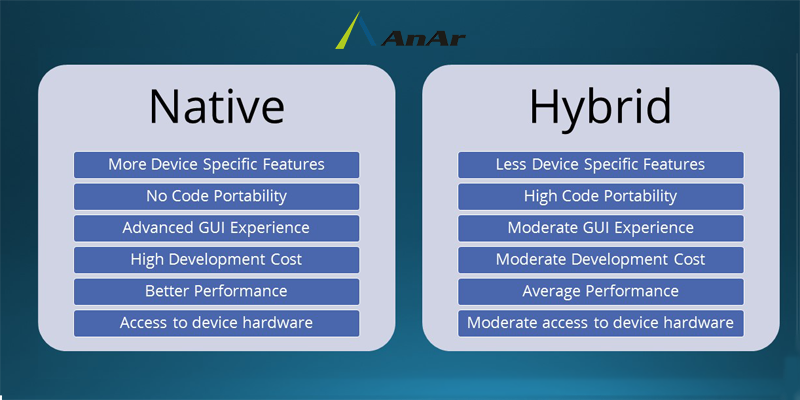
The smart phone segment is witnessing a very rapid growth in recent times. This is mainly due to its ease…
DevOps seeks to bridge the development and operations divide through the establishment of a culture of trust and shared interest…